Private Internet Access is one of the most popular VPN providers on the market. With so many people using VPNs these days, many might not know of certain features that can improve their experience. That’s why we’ve compiled 5 features available from PIA that you might not have known about.
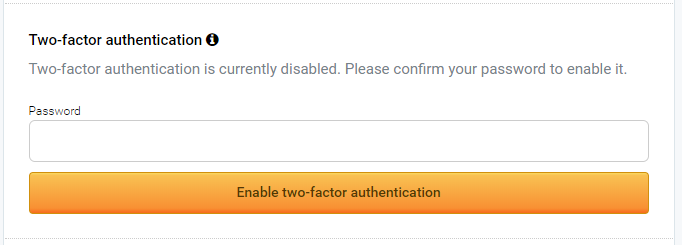
5. You can enable 2FA For Your Account
While this might not be a very exciting feature, you can enable 2FA for your account. That’s especially important if you want to make sure that your account is secure. Having someone else use your account and IPs can be detrimental to your security, which you are already trying to increase by using a VPN in the first place.
To enable 2FA, go to your Client Control Panel on PIA’s website. Scroll down to the 2FA section and enter your password. It will show a QR code that you can scan with 2FA apps such as Google Authenticator. Once you scan the code your 2FA app will show you a code which you will need to input on the website. After that you should be all set.
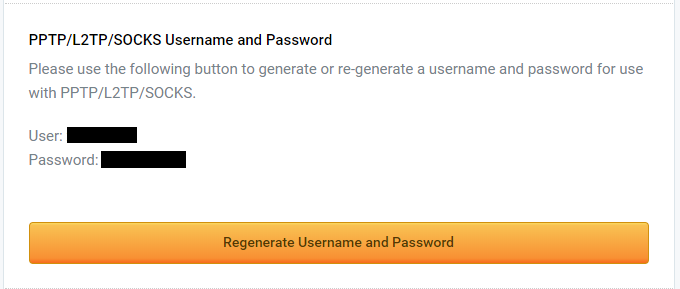
4. SOCKS5 Proxies
For those not familiar with SOCKS5 proxies, they essentially a more secure VPN connection. SOCKS5 proxies require additional authentication which ensures that nobody else has access to the server you are proxying through.
Let’s say you want to access your exchange via VPN, if someone has access to that VPN proxy your traffic can be compromised. However, if you access your account using a SOCKS5 proxy, your traffic is encrypted and secured.
The most common use for PIA’s proxy service is torrenting. Software like uTorrent and BitTorrent support SOCKS5 proxies.
You can enable your SOCKS5 proxies via the Client Control Panel below where you can enable 2FA. Click the button to generate a new username and password for your SOCKS5 proxies.
When you want to use the proxy, use the following settings:
Host: proxy-nl.privateinternetaccess.com
Port: 1080
Proxy Type: SOCKS5
Username: the one generated above
Password: the one generated above
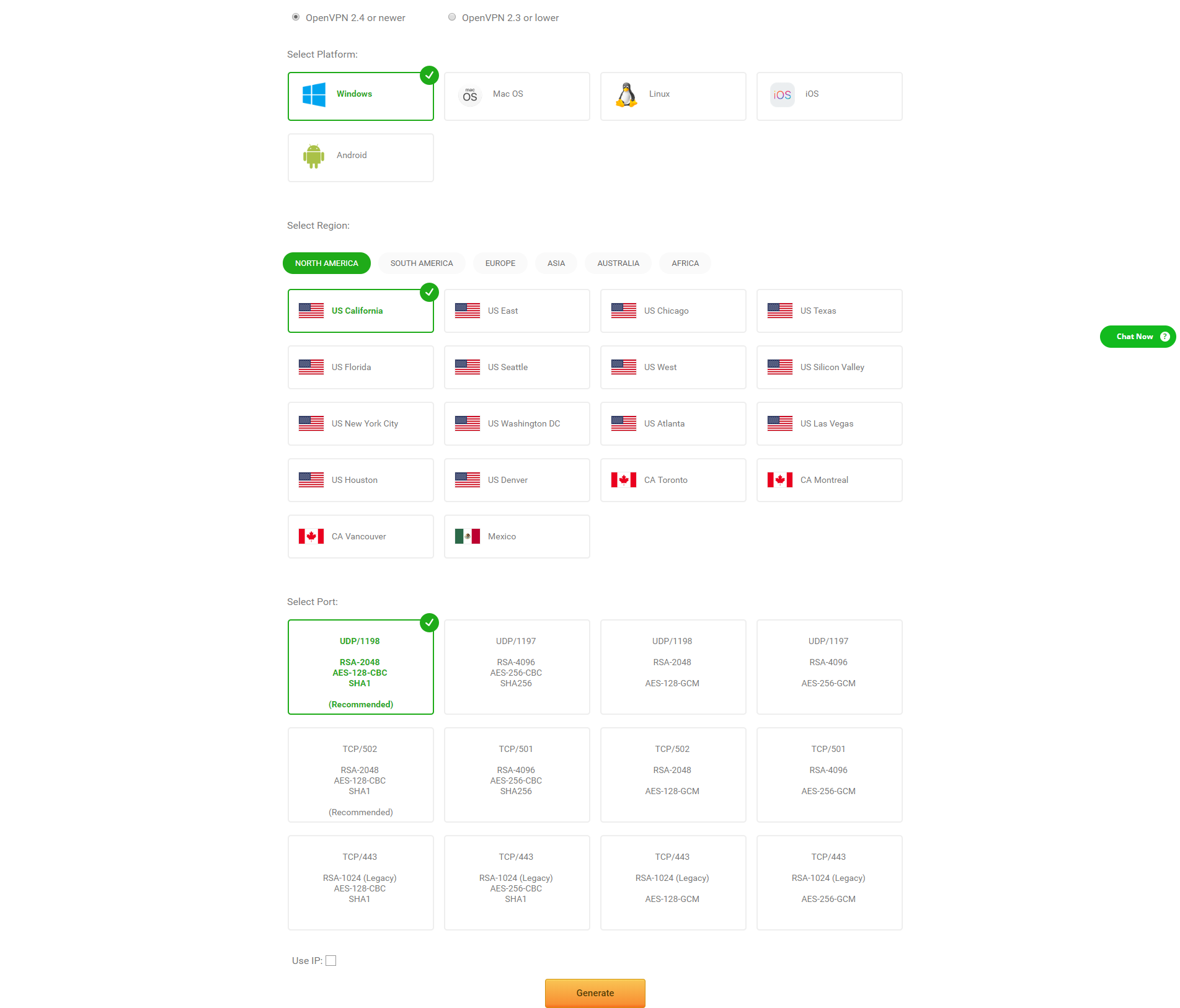
3. OpenVPN Generator
If you don’t want to use PIA’s VPN client, you can use the open source OpenVPN software to connect to Private Internet Access’ servers. If you scroll down in the Client Control Panel, you can click on the OpenVPN Generator.
This will take you to a page where you can select the type of connection and the area you would like to connect to. Once you hit generate you will download a .ovpn file which you can import into any OpenVPN client.
This could be useful if you want to connect to the VPN with multiple connection or tunnel multiple VPNs. Moreover, using .ovpn provides you with much more options for your connections.
2. VPN Killswitch
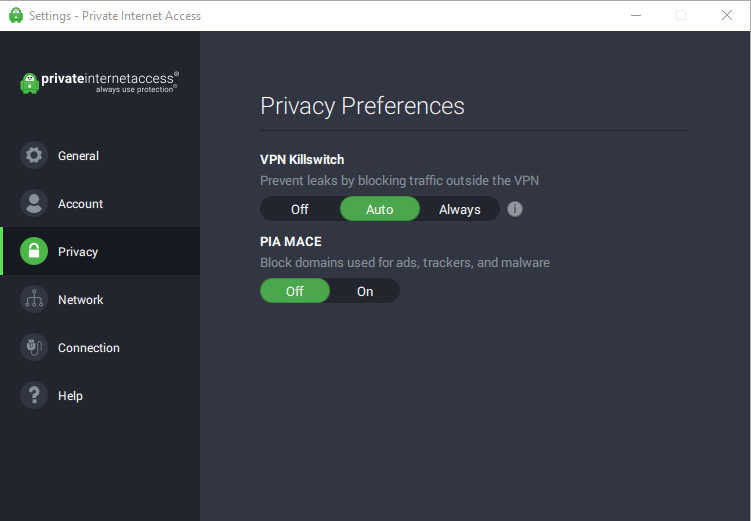
If you navigate to the privacy settings in your PIA client, you will find an option called VPN Killswitch. There are three settings available, Off, Auto, and Always.
You definitely don’t want to turn that off, and the default setting of Auto means the VPN will block all traffic outside of it as long as it’s on. However, if you are looking to be protected 24/7 even when you forget to turn your VPN on, setting it to Always will ensure that any traffic outside the VPN is blocked even when it’s off.
1. PIA Mace
Below the VPN Killswitch option, you will find the PIA Mace. The default option is set to off, but you do want to turn it on as it blocks known domains that are associated with ads, trackers, and malware.
PIA Mace is essentially a better version of Ad Block. It tricks the ad servers into preventing your browser from replying to tracking requests. The benefit of PIA Mace over Ad Block include not having to install any extensions, faster response time, and the benefit of saving your battery if you are using the mobile VPN client.
Special Mentions
We have two more special mentions that we didn’t include in our original list because they aren’t exactly features. Private Internet Access also has both Android and iOS Mobile Apps.
If you are serious about protecting your online privacy, you should have a VPN on your mobile phone as well. Moreover, all the features described above are still available on the mobile versions of the app.
If you like these features and want to know more about PIA, make sure to check out our Private Internet Access VPN Review.
The post 5 Features You Might Not Have Known About Private Internet Access VPN appeared first on NullTX.

Cryptocurrency is a digital currency that uses encryption (cryptography) to regulate the generation of currency and verify the transfer of funds, independently of a central bank. Cryptography is the practice and study of techniques for secure communication in the presence of third party adversaries.
Blockchain 101 · Crytpo Currency Market
---------------------------------------------------
Trezor: Hardware Wallet
Binance: Exchange for Traders
Ledger Nano S: Hardware Wallet
Coinbase: Exchange for Investors
CoinSwitch: Wallet-to-Wallet Exchange